What Is a Firewall - An Easy Overview
In today's world, where computers and the internet have become an integral part of our daily lives, the need for cybersecurity has never been more important. As we rely more and more on technology to store and transmit sensitive information, the risk of cyber-attacks has increased significantly. Hackers, malware, viruses, and other types of cyber threats are constantly evolving, making it increasingly difficult to protect ourselves and our data.
One of the most basic and essential tools for protecting your computer network from cyber threats is a firewall. There are several types of firewalls to choose from, each with its own strengths and weaknesses. Understanding the different types of firewalls and how they work can help you choose the best option for your organization's specific needs. In the following sections, we will dive deeper into the various types of firewalls, why they are important, and how to configure them for maximum protection.
What is a firewall?
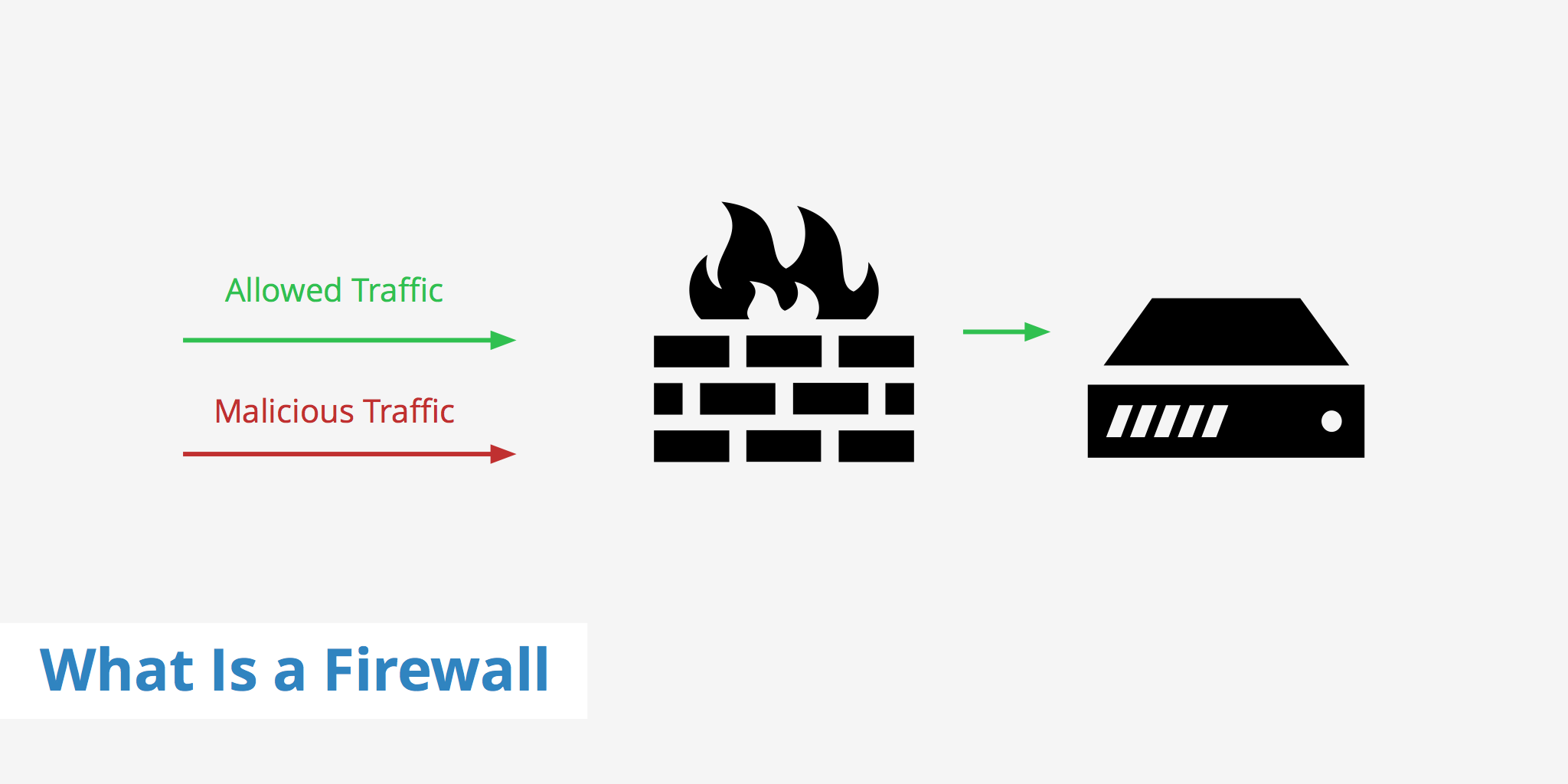
In simple terms, a firewall is a network security device that monitors and filters incoming and outgoing network traffic based on an organization's previously established security policies. It acts as a barrier between your internal network and the Internet, allowing only authorized traffic to pass through while blocking unauthorized traffic.
A firewall can be either a piece of software or hardware that helps control incoming and outgoing traffic by keeping unwanted traffic out. Hardware-based firewalls are physical devices that are placed between your internal network and the Internet. They typically have multiple Ethernet ports that connect to your network and the Internet, and can be configured through a web interface or a command-line interface. Software-based firewalls, on the other hand, are programs that are installed on your computer or server, and they monitor and filter network traffic that passes through your computer or server.
By defining a set of rules, the firewall is able to determine what traffic should be blocked and what can safely pass through. Firewalls have been around for some time, however, are becoming more and more prevalent as the number of cyber attacks increases, especially in terms of DDoS.
Why do you need a firewall?
The Internet is a dangerous place, and there are many threats lurking around every corner. Hackers, viruses, worms, and other types of malware are constantly trying to gain access to your network and steal your valuable data. A firewall can help protect your network by blocking unauthorized traffic, preventing malware from entering your network, and alerting you to potential security breaches.
Firewalls are also important for compliance with regulatory requirements. Many industries, such as healthcare, finance, and government, are required to meet certain security standards to protect sensitive data. Firewalls can help organizations comply with these standards by providing a first line of defense against unauthorized access to sensitive information.
Types of firewalls
There are a few types of firewalls to choose from when wanting to protect your network from malicious incoming/outgoing traffic. Each type is explained in detail below.
Packet firewalls
Packet firewalls are the earliest generation of firewall technology. Using this method, the firewall looks at the network packet's source and destination address, protocol, and destination port number. It will then check this information against the set of rules defined and if any of the information infringes upon those rules then the packet is dropped from the network. Packet filtering firewalls are fast and efficient, but they are also vulnerable to attacks that use packet fragmentation or other techniques to bypass the rules.
Packet firewalls work mainly on the first 3 OSI model layers while stateful firewalls work on the first 4 and the 4th layer. Furthermore, application layer firewalls work on the 7th layer. The image below shows an overview of the different OSI layers.
Stateful inspection firewalls
Stateful inspection firewalls are more secure than packet filtering firewalls, but they are also more complex and slower. These type of firewalls record all connections passing through and are able to determine whether the packet is part of a new connection, existing connection, or not part of any connection at all.
If the packet is not part of any existing connection, it must be checked against a set of rules to determine whether or not it is malicious. To speed up this process of stateful packet inspection, packets are cross-checked with the firewall's state table and if they are a part of an existing connection they can pass through without any further analysis.
Application layer firewalls
Application layer firewalls are the third generation of firewalls. As the name implies, application layer firewalls work on the application level of the TCP/IP stack (the 7th level). The need for application layer firewalls increased as hackers turned their attention from attacking the networking resources behind a server towards attacking the application itself.
Application layer firewalls work by examining all incoming and outgoing packets and blocking those that are deemed malicious. Filtering rules are usually set in place by the web developer or security service and can be modified to provide stronger protection or let more packets pass through.
Proxies
A Proxy firewall acts as an intermediary between the client and the server and determines which traffic should pass through. If your content delivery network protects against DDoS attacks you can think of this as a proxy firewall wince the client makes a request to the CDN's edge server and the CDN determines at that point whether or not the client's packets should be dropped or not based on certain rules.
Next-generation firewall
Next-generation firewalls are the latest evolution of firewalls, and they combine the features of packet filtering firewalls, stateful inspection firewalls, and application-level gateway firewalls into a single device. They can perform deep packet inspection, intrusion prevention, and application identification and control, and they can provide real-time threat intelligence and reporting. Next-generation firewalls are highly customizable and scalable, but they are also the most expensive type of firewall.
Hardware vs software firewalls
The difference between hardware and software firewalls is quite simple. The following section explains both.
Hardware firewalls
Hardware firewalls are actual hardware systems tasked with the sole purpose of mitigating malicious traffic. Hardware firewalls are intermediaries and placed between a network (e.g. a company and the Internet). Large companies sometimes setup hardware firewalls themselves so that all traffic passes through their own firewall before going to the server. Alternatively, a dedicated security service can be used.
Software firewalls
A software firewall is designed to run on a single machine and is typically seen on personal computers. These types of firewalls help ensure that unwanted third-parties don't compromise the machine. Software firewalls do this by preventing communication over risky ports (i.e. those that aren't used often to receive information).
How do firewalls work?
As highlighted in the sections above, there are a few different types of firewalls and how they work is different based on the type used. However, at a high-level they all basically follow the same process:
- A client request is made to a server
- The client's network packets are passed through the website's firewall
- The firewall checks the packets against its list of rules
- If the packets pass the rules it goes through to the server
- If the packets fail one of the rules it is dropped
- Rinse and repeat
Configuring a firewall
Configuring a firewall can be a complex task, but there are some basic steps that you can follow to ensure that your firewall is set up correctly:
1. Define your security policies
Before you configure your firewall, you need to define your security policies. These policies will determine what traffic is allowed to pass through your firewall and what traffic is blocked. Your policies should be based on the specific security requirements of your organization.
2. Determine your network topology
To configure your firewall, you need to know the topology of your network. This includes the IP addresses of your devices, the network segments they are on, and how they are connected to each other.
3. Choose the right firewall for your needs
As we discussed earlier, there are several types of firewalls. You need to choose the right type of firewall for your needs, based on factors such as the size of your network, the level of security you require, and your budget.
4. Configure your firewall
Once you have chosen your firewall, you need to configure it according to your security policies. This includes setting up rules to allow or block specific types of traffic, configuring NAT (Network Address Translation) and port forwarding, and setting up VPN (Virtual Private Network) connections.
5. Test your firewall
After you have configured your firewall, you need to test it to make sure that it is working correctly. You can use tools such as port scanners and vulnerability scanners to test your firewall and identify any weaknesses.
6. Monitor your firewall
Finally, you need to monitor your firewall on an ongoing basis to make sure that it is providing the protection that you need. This includes monitoring your logs for suspicious activity, reviewing your security policies periodically to make sure they are up to date, and staying informed about new threats and vulnerabilities.
Should you be using a firewall?
In regards to whether or not you should use a firewall, it comes down to your specific use-case. Macs are actually shipped with firewalls turned off because a standard Mac OS X system doesn't have potentially vulnerable services listening by default. On the other hand, Windows does have the firewall turned on by default, which in most cases is a good idea to leave enabled.
As for web-based firewalls, that's a bit of a tricky question. On one hand, if you enable a firewall your site will be more secure and less vulnerable to attack, however, on the other hand, enabling a firewall will come at a cost in terms of performance. Checking packets takes time and can slow down the performance of a website. Therefore, before deciding whether or not you need a firewall, you should audit your site and see if it has ever been hit before or if you're in a space that is susceptible to cyber attacks. If so, it might be time to enable a firewall for your application.
Hopefully, this article has helped you better answer the question of "what is a firewall". If you would like to learn more about web security, check out the related articles section below.