HTTP Strict Transport Security
What is HTTP Strict Transport Security?
HTTP Strict Transport Security (HSTS) is a security enhancement that restricts web browsers to access web servers solely over HTTPS. This ensures the connection cannot be establish through an insecure HTTP connection which could be susceptible to attacks. HSTS is defined in the response header as Strict-Transport-Security and once the supported browser receives that header it knows to deliver all information over HTTPS.
How it works
In order to set up HTTP Strict Transport Security, it must first be enabled on your origin server which we will discuss how to do later in the article. Once it is enabled on the server side, the web server will begin adding an additional response header to tell the browser to communicate solely over HTTPS. The response header will look similar to this:
Strict-Transport-Security: max-age=31536000; includeSubDomains; preload.
max-agedefines the time in seconds for which the web server should only deliver through HTTPS.includeSubDomainsis optional. This will apply HSTS to all the site's subdomains as well.preloadis also optional. The site owner can submit their website to the preload list which is a list of sites hardcoded into Chrome as being HTTPS only.
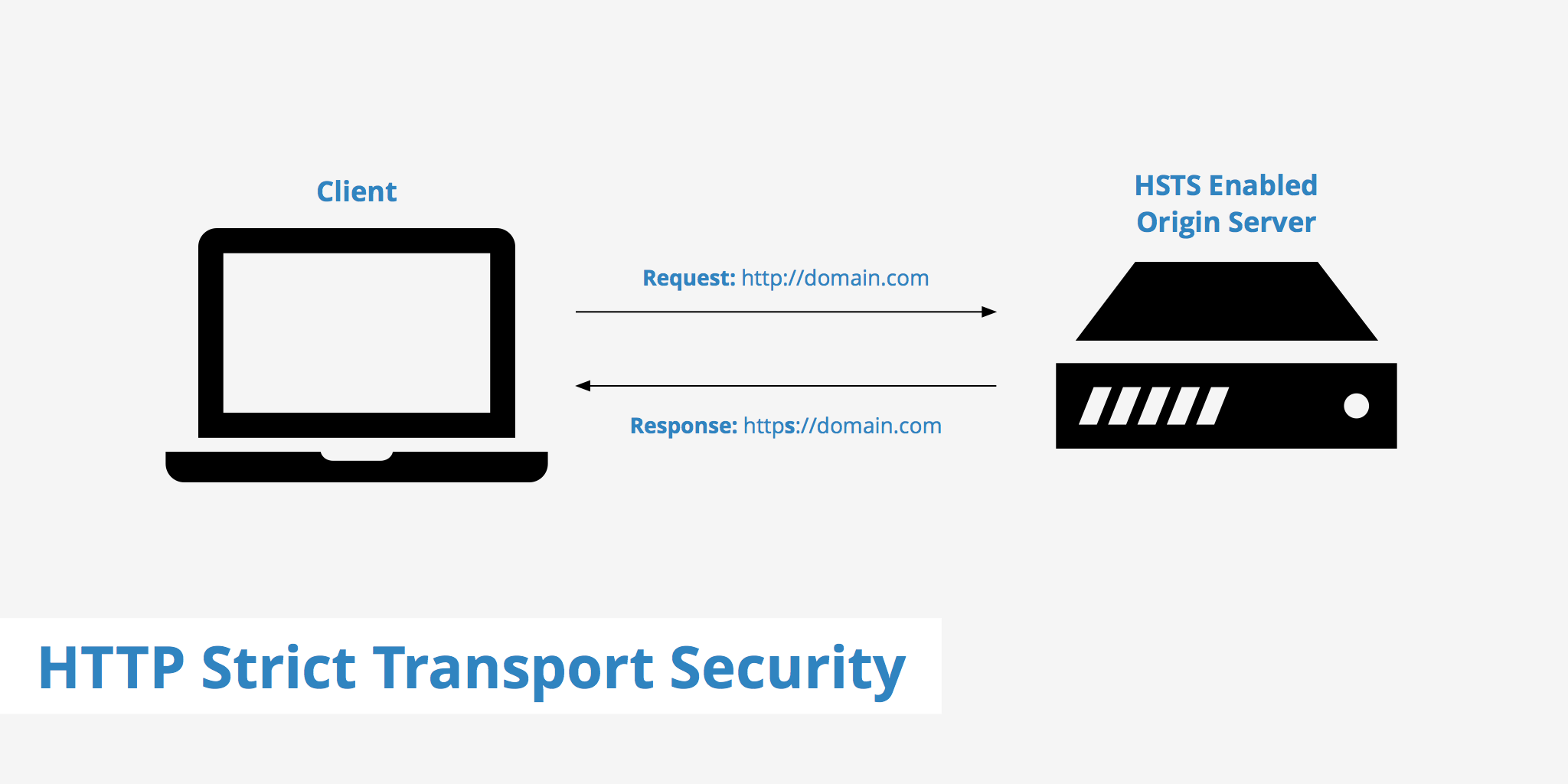
When the HTTP Strict Transport Security header is present on a particular website and you access it for the first time over HTTPS, the browser takes note and ensure any future access to http://domain.com will be modified to https://domain.com. The browser will do so as long as the expiration time does not run out. However, each time the header is delivered to the browser, the expiration time is updated and refreshed, helping the prevention of expiration.
In the case that a secure connection cannot be established, an error message will be shown and the browser will not allow the user to access the site.
Threats it protects against
Failing to connect to a secure HTTPS connection can be quite detrimental in some cases such as when accessing your online banking. According to OWASP, the following three points are common threats that HSTS is able to protect against.
- Attackers using an invalid certificate in the hopes the user will accept the bad cert.
- Old bookmarks that contain
http://or manually enteredhttp://URLs that can be vulnerable to an attack. - Sites claiming to be fully HTTPS serving HTTP content.
Due to HSTS's strict rules, the above threats will no longer be relevant as it doesn't allow the use of insecure HTTP.
Enabling HTTP Strict Transport Security on your server
Adding HSTS to your server is easy and can be done in just a couple of steps. See below for instructions on enabling it on Apache and Nginx.
Apache
In order to enable HSTS on your Apache server, you must edit your configuration file and add the following to Virtual Host.
<VirtualHost 67.89.123.45:443>
Header always set Strict-Transport-Security "max-age=63072000; includeSubdomains; preload"
</VirtualHost>
Nginx
To enable HSTS on Nginx, add the following to the server block.
add_header Strict-Transport-Security "max-age=63072000; includeSubdomains; preload";
In order to check if the HSTS header is being delivered as a response header from your origin server, you can run a curl command, for example:
curl -I http://keycdn.com/css/all.min.css
HTTP/1.1 301 Moved Permanently
Server: nginx
Date: Mon, 02 Nov 2015 19:07:45 GMT
Content-Type: text/html
Content-Length: 178
Connection: keep-alive
Location: https://www.keycdn.com/css/all.min.css
Strict-Transport-Security: max-age=31536000; includeSubdomains; preload
Browser support
All major up to date browsers currently support the use of HSTS with the exception of Opera Mini and versions previous of IE 11. So if you're planning on using HTTP Strict Transport Security on your origin server it's fairly safe to say most of your users' browsers will support it.
Summary
In summary, HTTP Strict Transport Security is powerful and useful feature to implement for keeping your website visitors safe. Although insecure HTTP content can be delivered for a multitude of reasons, HSTS helps eliminate that risk, leaving attackers unable to intercept communication.