Quick Guide to DNSSEC
As we spend more and more of our lives online, the security of our online communications becomes increasingly important. From banking and shopping to social media and email, we rely on the internet to connect us to the people and services we need. There are many ways for hackers to take advantage of the infrastructure that's used to deliver web assets around the world. But how can we be sure that our online communications are secure?
One technology that can help is DNS Security Extensions (DNSSEC) - a set of protocols that add an additional layer of security to the domain name system. In this guide, we'll take a closer look at DNSSEC, what it is, and how it works. Whether you're a business owner looking to secure your online transactions or an individual concerned about online privacy, DNSSEC is an important security technology that's worth understanding. So let's dive in!
What is a DNS?
Words are easier to remember than numbers, which is why we have the Domain Name System, or DNS. The DNS translates domain names, like www.google.com, into numeric IP addresses. Translation takes place within a DNS server where domain name information is stored.
While the DNS has made life easier in many ways, it can be the source of security breaches. Fortunately, extensions exist to mitigate vulnerabilities. These security protocols are collectively called domain name system security extensions, or DNSSEC.
How does a DNS work?
The DNS is often referred to as the "phone book of the internet" because of how it looks up IP addresses. DNS translation takes place in steps, and it starts at the root Zone, or the top level of the directory service. For example, when you enter www.google.com into a browser, the DNS resolver asks the root Zone directory where to look for the ".com" directory. Next, the resolver asks the ".com" directory where to find the "google.com" directory. Finally, it asks the "google.com" directory where to find "www.google.com" for the full requested IP address. Hackers can hijack any step of this process, which is why we need DNSSEC.
To learn more about how the DNS works, check out our complete what is a DNS guide.
What is DNSSEC?
The primary purpose of DNSSEC is to make sure that internet users aren't redirected to fraudulent IP addresses. The protocols protect against man-in-the-middle attacks, pharming, cache poisoning and other types of cyber attacks by matching cryptographic signatures to DNS records. It does not, however, defend against DDoS attacks.
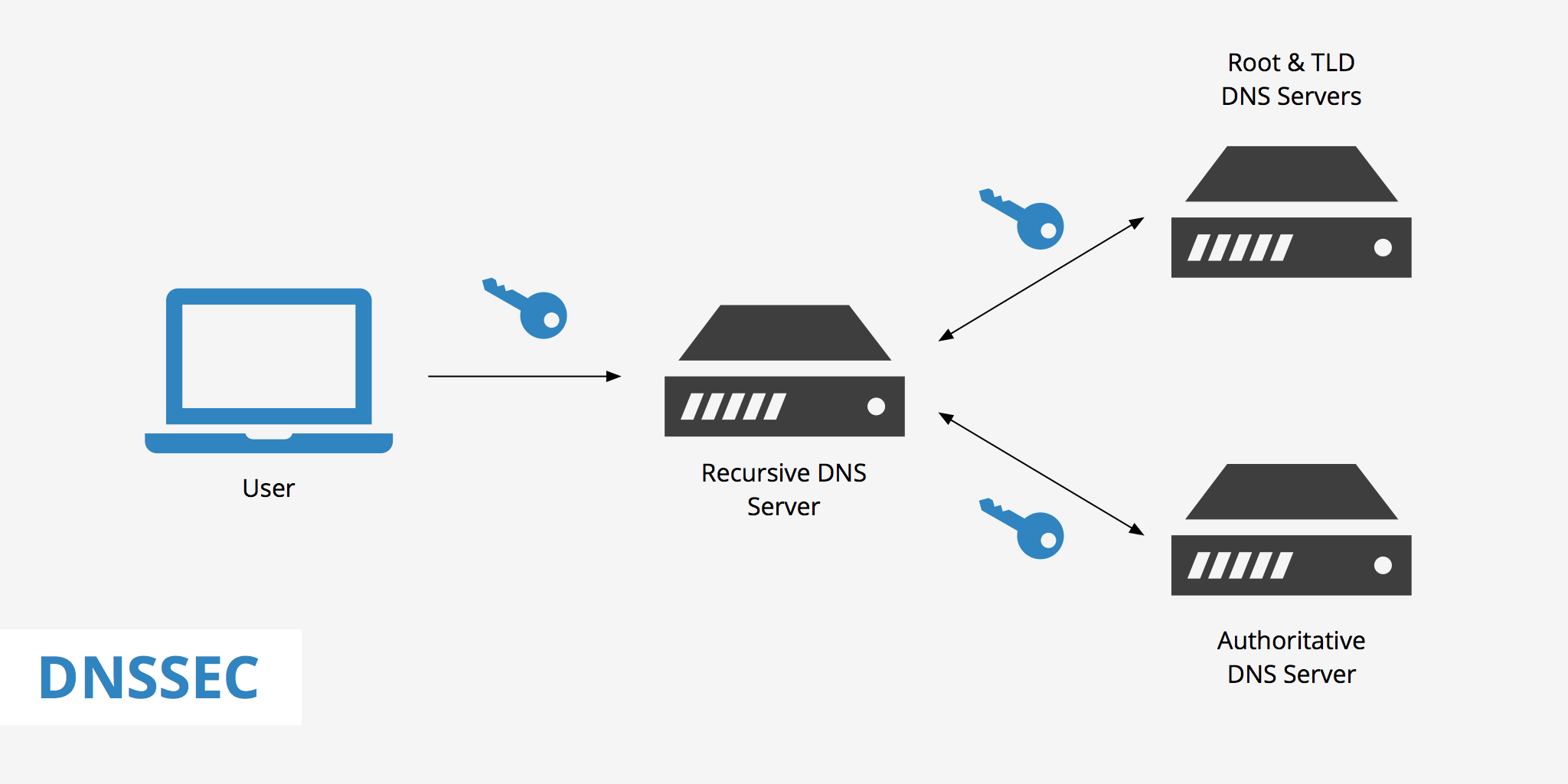
Digital signatures reside on the DNS server and are verified by a resolver. When a user enters a web address into their browser, the resolver checks to make sure that the digital signatures embedded in the data are identical to those residing in the master DNS server. If so, the connection can commence. DNSSEC must be deployed at each step from the root Zone to the final domain name destination.
Why is DNSSEC important?
DNSSEC provides a way to authenticate the source of DNS information and verify its integrity. It can prevent attackers from spoofing DNS responses, redirecting traffic to malicious servers, or intercepting DNS queries.
By using DNSSEC, you can be sure that the website you're trying to reach is the one you intended to visit, and that your traffic isn't being intercepted or redirected. This is particularly important for online transactions, where you want to be sure that you're communicating with the right server and not a fake one.
How does DNSSEC work?
DNSSEC uses a hierarchical system of public key cryptography to sign DNS responses. Each DNS zone (a section of the DNS namespace, like "example.com") has a public and private key pair. The private key is used to sign the DNS responses, while the public key is used to verify the signatures.
When you make a DNS query, the DNS server includes a digital signature in the response that proves the authenticity of the information. Your computer can then use the public key of the zone that the DNS response came from to verify the signature and ensure that the information is authentic.
Pros of enabling DNSSEC
- Added protection against MITM attacks, DNS spoofing, cache poisoning, etc
- Increases trust for online activities such as ecommerce, VoIP, etc
- Enhanced privacy
Cons of enabling DNSSEC
- Added complexity both on the client and server side
- Incompatibility with some older DNS software and hardware
- Additional costs in the event that you move from managing your own DNS to managed DNS provider to reduce complexity
- Potential for misconfiguration and human error
Implementing DNSSEC
Now that you know why DNSSEC is important and how it works, let's take a look at how you can implement it.
Step 1: Check if your domain is already signed
The first step is to check if your domain is already signed. You can do this by using a DNSSEC validator tool like Verisign's DNSSEC Analyzer. Simply enter your domain name, and the tool will check if your domain has DNSSEC enabled and whether it's configured correctly.
Step 2: Sign your domain
If your domain isn't signed, the next step is to sign it. The process of signing your domain involves generating a public and private key pair, creating a signature for your DNS records, and publishing your public key in the DNS.
Most DNS hosting providers offer DNSSEC support, and you can usually enable it through your account settings. Alternatively, you can use a DNSSEC signing tool like OpenDNSSEC or BIND to sign your domain.
Step 3: Configure your DNS zone
Once your domain is signed, you'll need to configure your DNS zone to include the necessary DNSSEC records. These records include:
- DNSKEY: This record contains the public key for the DNS zone.
- DS: This record contains a hash of the DNSKEY record that's stored in the parent zone. This is used to establish a chain of trust between the child and parent zones.
- RRSIG: This record contains the digital signature for the DNS records in the zone.
- NSEC or NSEC3: These records are used to prove that a DNS record doesn't exist, which can help prevent certain types of attacks.
- CDNSKEY and CDS: facilitates DS update requests between child and parent Zones
These records can be accessed in the same way as a regular DNS record such as a CNAME or A record however they are used to digitally sign a domain. DNSSEC also involves two main types of keys:
- Zone-signing keys, or ZSKs: contain both a public and private key portion and validate specific record sets within a Zone
- Key-signing keys, or KSKs: sign DNSKEY records
Each signed nameserver possesses one public key and one private key. When a client makes a request, the data they transmit is signed with a private key, which the recipient then opens with a public key. If a third party attempts to intervene without the public key, the recipient knows that the data is fraudulent. Because DNSSEC doesn't come with any encryption algorithms, it can't provide data confidentiality; it just helps the DNS server verify the authenticity of data requests.
Your DNS hosting provider should have instructions on how to add these records to your DNS zone. You'll also need to update your registrar's records with the DS record from your DNS zone.
Step 4: Test your DNSSEC configuration
Once you've configured your DNS zone, it's important to test your configuration to make sure it's working correctly. You can use a DNSSEC validator tool like the Verisign's DNSSEC Analyzer to check your domain's DNSSEC configuration.
These tools will check your domain's DNSSEC records and verify that they're configured correctly. If there are any issues, they'll provide guidance on how to fix them.
Step 5: Monitor your DNSSEC configuration
Finally, it's important to monitor your DNSSEC configuration regularly to make sure it's still working correctly. DNSSEC is a complex system, and there are many potential points of failure.
You can use tools like Zonemaster to monitor your DNSSEC configuration and receive alerts if there are any issues. It's also a good idea to set up alerts for changes to your DNS records or zone file, as these can indicate potential security issues.
Summary
Unlike HTTPS, which actually encrypts web traffic, DNSSEC simply allows DNS servers to identify and turn away potential malefactors.
As for DNSSEC deployment, it is still in the growing process and even if you wanted to implement it, most top-level domains don't currently support it. As it currently stands, the benefit-cost ratio does not weigh in the favor of DNSSEC simply because it is still too early. The lack of knowledge and the incompatibility in client/server side technology makes it difficult to adopt.
However, as security concerns continue to plague the Internet, perhaps the adoption rate of DNSSEC will continue to grow. While DNSSEC doesn't address all of our internet security woes, full deployment makes the directory lookup process safer for everyone.