What Is DNS Spoofing?
Have you ever wondered how your computer knows where to find a website when you type in a domain name? The answer lies in a system called the Domain Name System, or DNS for short. However, this system is not without its flaws. One such flaw is DNS spoofing, a form of cyber attack that can have serious consequences for both individuals and businesses.
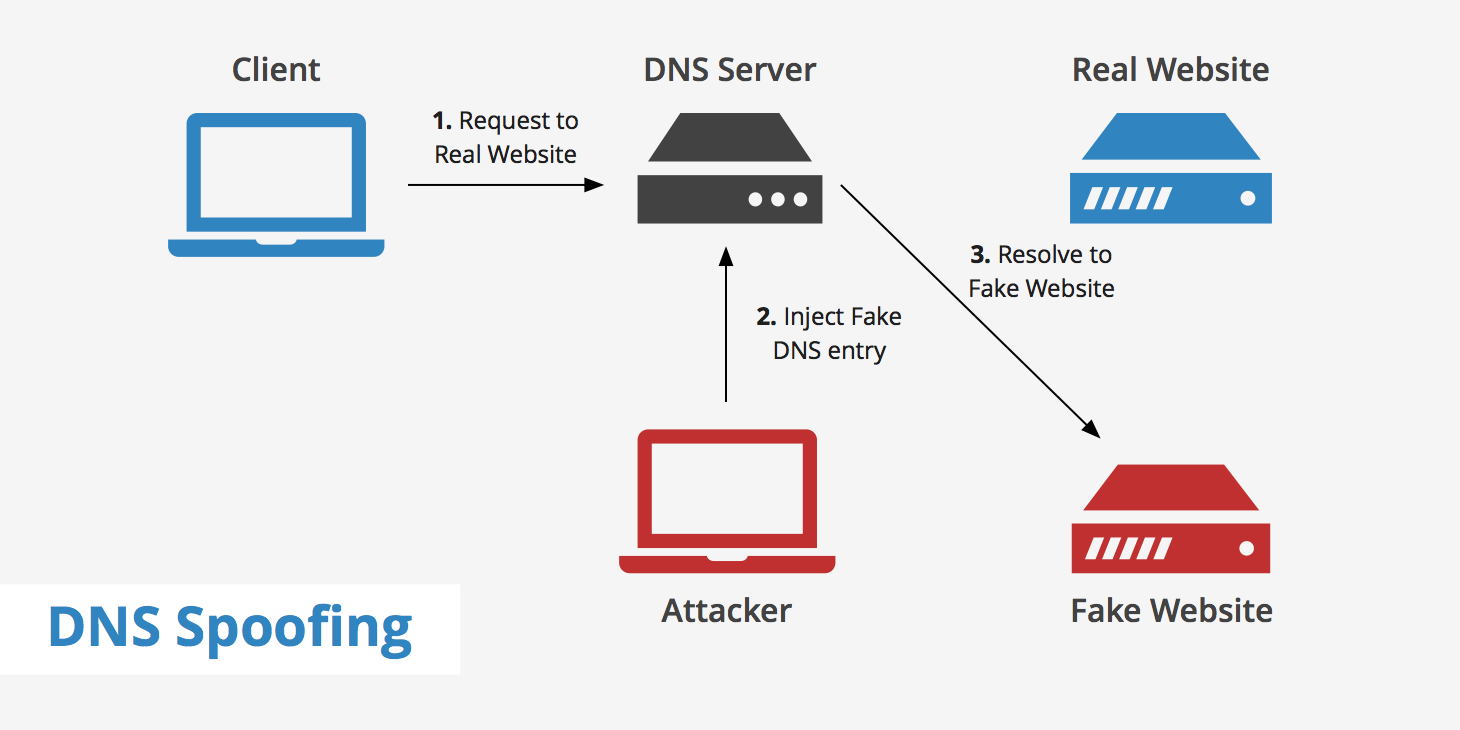
DNS spoofing occurs when a particular DNS server's records of "spoofed" or altered maliciously to redirect traffic to the attacker. This redirection of traffic allows the attacker to spread malware, steal data, etc. For example, if a DNS record is spoofed, then the attacker can manage to redirect all the traffic that relied on the correct DNS record to visit a fake website that the attacker has created to resemble the real site or a different site completely.
In this article, we'll explore what DNS spoofing is, how it works, and how you can protect yourself against it.
How does normal DNS communication work?
To understand DNS spoofing, we first need to understand what DNS is and how it works. A DNS server is used for the purpose of resolving a domain name (such as keycdn.com) into the associated IP address that it maps to. Once the DNS server finds the appropriate IP address, data transfer can begin between the client and website's server. The visualization below shows a how this process takes place at a high level.
When you type a domain name into your web browser, your computer sends a request to a DNS server asking for the IP address associated with that domain name. The DNS server then looks up the IP address and sends it back to your computer, allowing you to connect to the website you want to visit.
Once the DNS server finds the domain-to-IP translation, it will cache it so that upon subsequent requests for that domain, the DNS lookup will happen much faster. However, this is where DNS spoofing can become a real problem since a false DNS lookup can be injected into the DNS server's cache thus altering the visitors' destination.
What is DNS Spoofing?
DNS spoofing is a type of cyber attack in which a hacker intercepts DNS requests and sends back false information in response. For example, if you try to visit google.com, a hacker could intercept your DNS request and send back a fake IP address that leads to a malicious website instead.
The purpose of DNS spoofing is usually to redirect users to a fake website that looks like the real one. This is known as a phishing attack, and it can be used to steal sensitive information such as login credentials, credit card numbers, and more. In some cases, DNS spoofing can also be used to redirect users to websites that are infected with malware, which can infect their computers and steal information or cause damage.
How does DNS spoofing work?
DNS spoofing works by intercepting DNS requests and sending back false information. There are several ways that hackers can do this:
- DNS cache poisoning
- Compromising a DNS server
- Implementing a man-in-the-middle attack
However, an attacker's end goal is usually the same no matter which method they use. Either they want to steal information, reroute you to a website that benefits them, or spread malware. The above methods are the most common types of DNS spoofing, which we will discuss in more detail below.
DNS cache poisoning
Since DNS servers cache the DNS translation for faster, more efficient browsing, attackers can take advantage of this to perform DNS spoofing. If an attacker is able to inject a forged DNS entry into the DNS server, all users will now be using that forged DNS entry until the cache expires. Once the cache expires, the DNS entry will return to normal as the DNS server will go through the complete DNS lookup process again. However, if the DNS server's software still hasn't been updated, then the attacker can replicate this error and continue funneling visitors to their website.
DNS cache poisoning can also sometimes be quite difficult to spot. If the malicious website is very similar to the website it is trying to impersonate, some users may not even notice the difference. Additionally, if the attacker is using DNS cache poisoning to compromise one company's DNS records in order to have access to their emails for example, then this may also be difficult to detect.
Compromising a DNS server
Compromising a DNS server involves hacking into a DNS server and changing the DNS records directly. This can be done through various methods, such as exploiting vulnerabilities in the server software or using social engineering to gain access to the server.
Once the attacker has access to the DNS server, they can change the IP address associated with a domain name to redirect traffic to a fake website. This type of attack can be especially dangerous because it can affect a large number of users at once, and the attack can be difficult to detect.
To protect against this type of attack, it's important to ensure that DNS servers are properly secured and that access is restricted only to authorized personnel. Regular security audits and updates can also help to prevent vulnerabilities from being exploited.
Implementing a man-in-the-middle attack
A man-in-the-middle (MITM) attack involves intercepting communications between two parties and manipulating the messages. In the case of DNS spoofing, an attacker could intercept DNS requests and responses and alter them to redirect users to a fake website.
To implement a MITM attack, the attacker would need to be able to intercept the DNS requests and responses. This can be done through various methods, such as intercepting traffic on a public Wi-Fi network or by gaining access to a user's router. Once the attacker has intercepted the DNS requests and responses, they can alter the responses to redirect users to a fake website. This type of attack can be difficult to detect because the user's device still believes that it is communicating with the real DNS server.
To protect against this type of attack, it's important to use HTTPS whenever possible, as this encrypts web traffic and makes it more difficult for attackers to intercept and manipulate. Using a VPN can also help to encrypt traffic and protect against MITM attacks.
How to prevent DNS spoofing
Fortunately, there are several steps you can take to protect yourself from DNS spoofing. We have already mentioned a few, but here they are all summarized:
- Use a reputable DNS provider - some DNS providers are more secure than others, so it's important to choose one that takes security seriously.
- Implement DNS spoofing detection mechanisms - it's important to implement DNS spoofing detection software. Products such as XArp help product against ARP cache poisoning by inspecting the data that comes through before transmitting it.
- Use encrypted data transfer protocols - Using end-to-end encryption via SSL/TLS will help decrease the chance that a website / its visitors are compromised by DNS spoofing. This type of encryption allows the users to verify whether the server's digital certificate is valid and belongs to the website's expected owner.
- Use DNSSEC - DNSSEC, or Domain Name System Security Extensions, uses digitally signed DNS records to help determine data authenticity. DNSSEC is still a work in progress as far as deployment goes, however was implement in the Internet root level in 2010. An example of a DNS service that fully supports DNSSEC is Google's Public DNS.
- Keep your software up to date - many DNS spoofing attacks exploit vulnerabilities in software, so it's important to keep your operating system, web browser, and other software up to date to ensure that any known vulnerabilities are patched.
- Be wary of suspicious emails and links - many DNS spoofing attacks are initiated through phishing emails or links that lead to fake websites. Always be wary of emails or links that ask for sensitive information or that seem too good to be true.
Summary
DNS spoofing can cause quite a bit of trouble both for website visitors and website owners. An attacker's main motive to carry out a DNS spoofing attack is either for their own personal gain or to spread malware. Therefore, as a website owner, it's important to choose a DNS hosting provider that is reliable and uses up to date security mechanisms.
Furthermore, as a website visitor it's just as important that you "be aware of your surroundings" in a sense that if you notice any discrepancies between the website that you were expecting to visit and the website that you are currently browsing, you should immediately leave that website and try to alert the real website owner.