How to Create an SSH Key
What is an SSH key?
SSH keys are an easy and secure way for computers to identify themselves when trying to establish a connection to a third party. Using SSH is more secure than just using a password alone as passwords need to be sent over a network which makes them susceptible to eavesdropping and they can be cracked by brute force attacks. When using an SSH key it is nearly impossible for it to be cracked by a brute force attack due to their complexity. Additionally, SSH keys are never actually transmitted over a network.
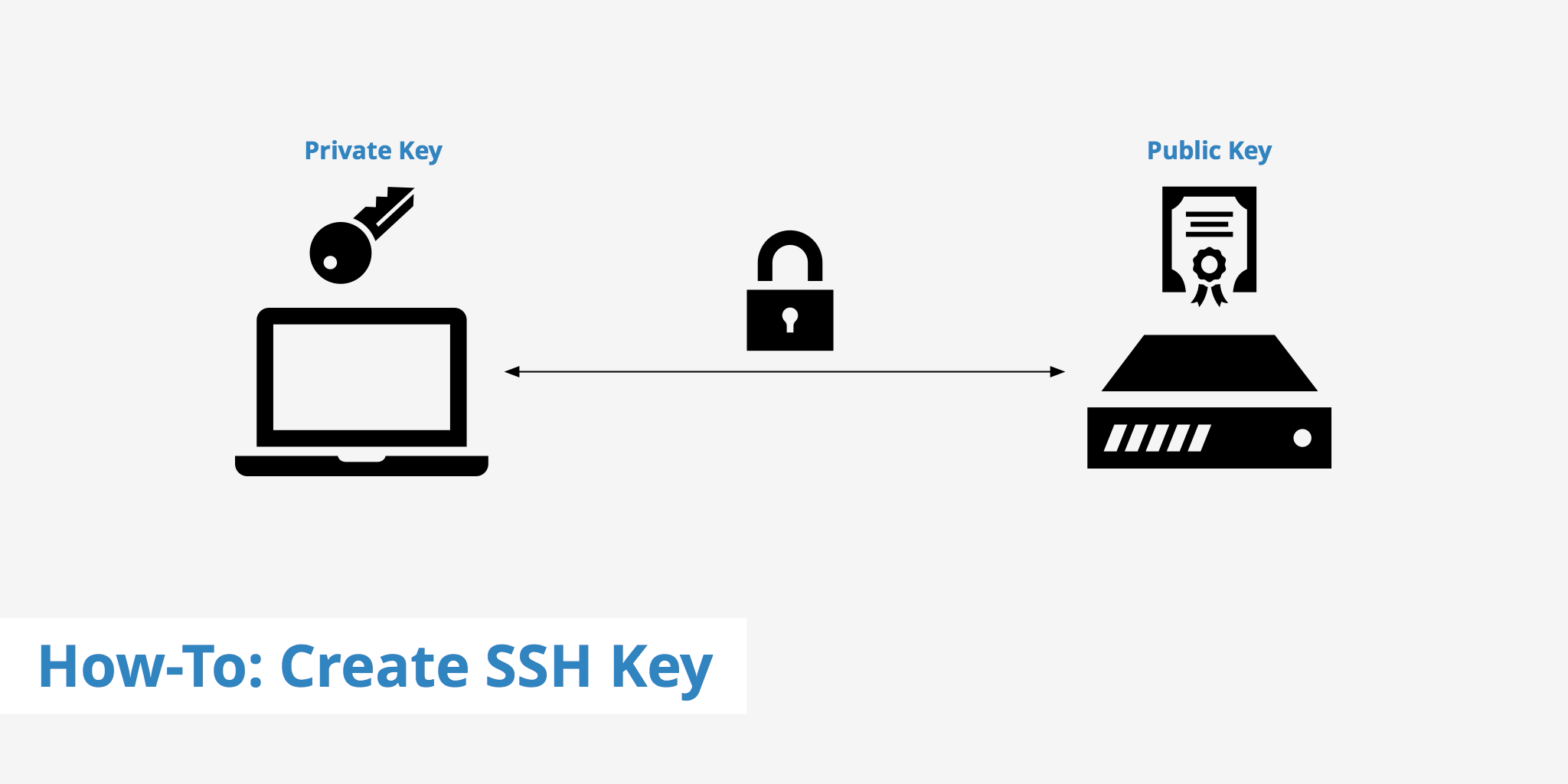
When a user creates an SSH key pair, a public and private key are both created. The way it works is let's say your client machine initiates a request to access a server. The server then sends back an encrypted message using your public key that can only be decrypted by your paired private key. Therefore in order for the connection between the client and server to be established, the private key must be able to decrypt the encrypted message that was sent from the server using your public key.
How to create an SSH key
Follow these steps in order to generate and start using your SSH key pair.
Step 1 - Make sure you don't already have an SSH key
Before creating your SSH key, you should first check to make sure you haven't already created one in the past. This can be done by using the following command:
cd ~/.ssh
ls
You should look for a pair of files named id_rsa.pub and id_rsa. These are known as your public and private keys respectively. If you don't see these files or don't even have a .ssh directory then you can move on to the next step.
Step 2 - Create SSH key
To create your SSH key, run the following command (note: if the following command fails, remove the -o option):
ssh-keygen -o
From here you will be given the option to enter a passphrase to access your private key. Implement this at your own discretion. Just know that if by chance an unauthorized user tries to access your private key they will need to enter your passphrase if you set one (making it more difficult for them to access your private key). The downside to this is that you will need to enter your passphrase every time you use the key pair. Once this step is complete, your keys will be stored in your home/user/.ssh directory.
Step 3 - Add your private key to your system
Make sure your private key is added to your system by running the following:
ssh-add /path/to/your/private.key
Step 4 - View your public key
You are now ready to copy your public key to a service that you would like to connect to via SSH. To view your public key, use the following command within the .ssh directory:
cat id_rsa.pub
This will display your public key which you can then copy and paste to your desired destination.
That's it! You now have a public and private key generated on your local machine and are able to use them to connect to third party services quickly and securely.